I’m sure everyone reading this is now aware of the threat that so-called ‘Ransomware’ attacks pose to businesses and consumers alike.
There is a perception that this is a new problem, but the first known attack actually happened way back in 1989 , distributed by post on a 5.25” disk (anyone else remember those?).
Back then, the best way to avoid being caught by ransomware was user awareness – a lot of people were suspicious of this unsolicited disk and didn’t install it.
Running an internal phishing test
With all of these attacks in the news recently, I was curious to see how the users in our company would react to a phishing email, and by extension if we were at threat from an attack.
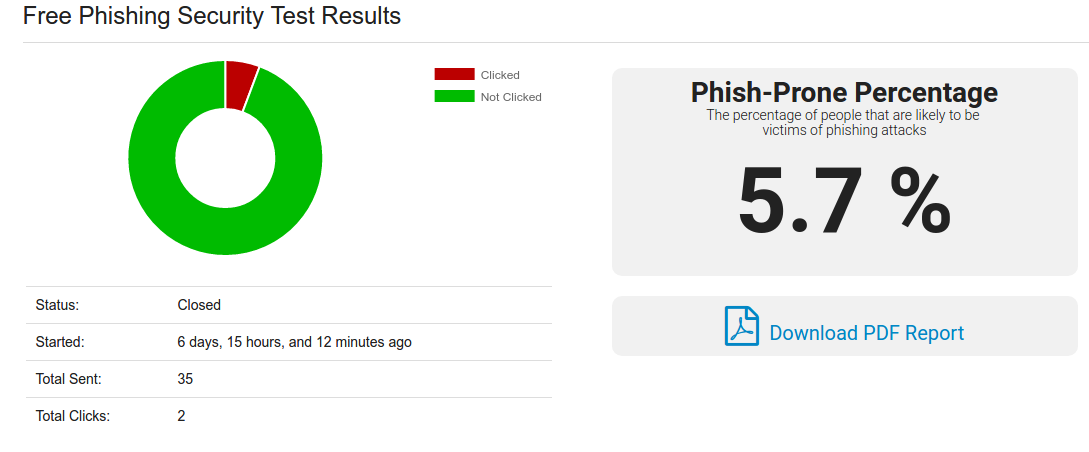
There are a number of sites out there providing a phishing simulation service, whereby they email a phishing email to a list of addresses, and report back on how many clicks those emails get. Most of them have a free trial option, and I ended up choosing the free ‘Phishing Security Test’ from www.knowbe4.com (they were the first result in Google when I looked for ‘phishing test’ – many others are available).
They suggest that 16% of phishing emails succeed, but it seems to me that if you get just one person clicking that suspicious link, then you’ve got an issue. Once that software is on your network, it can spread freely, and it doesn’t really matter at that point how it got there.
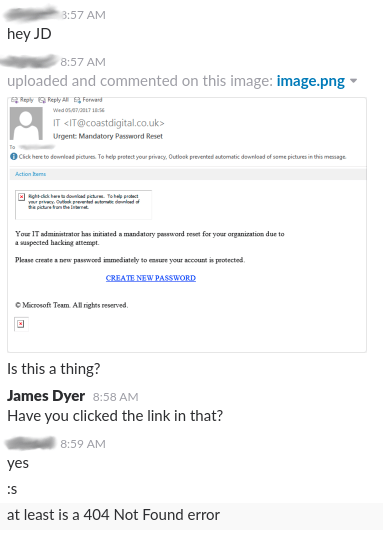
Here’s what got sent out to the users:
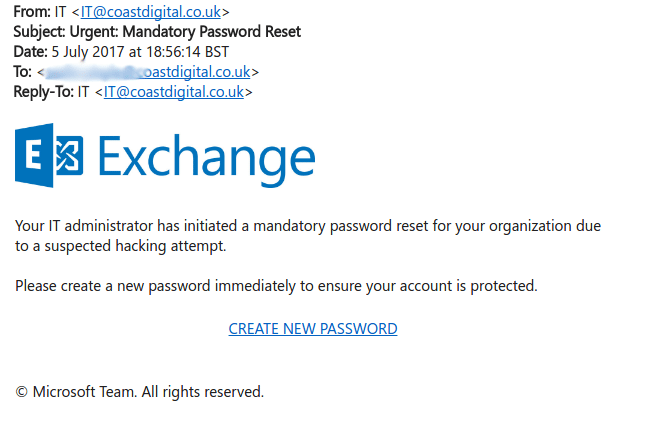
I had my first report of the suspicious email from one of my users about an hour later. Hadn’t clicked anything, thought it best to let me know that he’d received it. Perfect reaction to the email in my book. Perhaps all of my users would do that?
Silence from then until the next morning. Checked the dashboard at Knowbe4, which was showing that no-one had clicked – very encouraging. People started coming into the office, and started reporting it to me, also discussing the obvious phish on Slack (I did tell those who’d reported it to me that it was a test, asking them to remain quiet about it – seemed the best option really). Still at 0% click, and I was beginning to really hope that no-one would click the link in the email.
It only takes one (and we got two)
Not to be of course! About an hour later, the Knowbe4 dashboard reported a click. A few minutes after that, an email saying:
We’re now almost a week into this exercise, and I think it’s been useful. It’s gone better than I expected I think, I was fearful that we’d get a lot more than just 2 successes. Most people just deleted the mail, and a few forwarded it over to me to check if it was legitimate or not – I’m very encouraged by that, people are being paranoid about unexpected emails, and that’s one of the best protections you can have.